Advanced Packet Editor – TCP/HTTP Client-Server Proxy
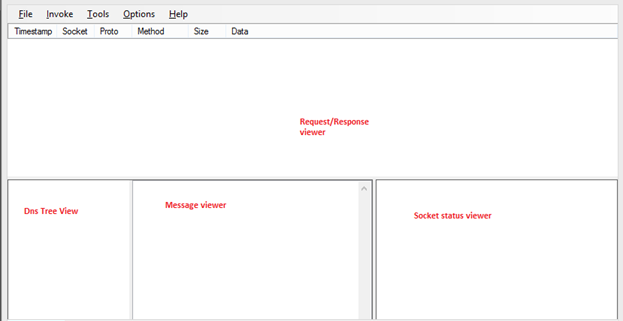
The Advanced Packet Editor (APE) is an open-source project for a TCP and HTTP-based proxy that allows you to intercept and manipulate communication between clients and servers.
We at AppSec Labs have taken the project, modified and improved it into a useful tool for application penetration testing.
This tool is under the GPL license (for more information: http://www.gnu.org/licenses/gpl-3.0.en.html)
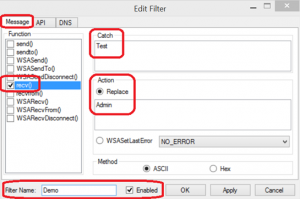
APE allows you to create internal and external filters, automatically catch and replace internally by defining rules.
For example, let’s say that we want to catch when the application receives the user named “Test” and change it to “Admin”.
We check the “recv()” function and set the application to catch “Test” and replace it with “Admin”. Then, we give our filter a name for future reference and enable it:
Figure 1 – Setting internal filters
Filters can also be set externally using an ad-hoc supplied python script. The script creates a server that enables customization of the applied filters.
APE shows sockets as they open and close and detailed information that is sent back and forth:
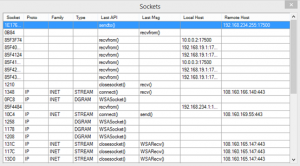
Figure 2 – Detailed information about Sockets
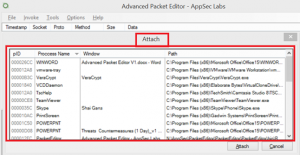
APE operates by injecting itself into a running process (“Attach”) or executing an application (“Open”) with APE already injected into it (note: this requires administrative privileges):
Figure 3 – Attaching APE into a running process
Once attached, filters that were set become active. Furthermore by using Invoke-> Freeze, we can freeze the current application.
APE also enables interaction with external tools such as Portswigger’s Burp Suite.
To enable this, run APE with administrative privileges and check “Listen to Requests” (Under “Tools” in the main menu).
For more details regarding the usage of APE, view documentation here.
The tool can be found here
Source code can be found here
Special thanks to http://www.packeteditor.com/ for developing the initial packet editor.



Leave a Reply
Want to join the discussion?Feel free to contribute!